
Date: 02 Oct 2018

Date: 02 Oct 2018
Keeping yourself safe online can be achieved easily with some good personal housekeeping habits, says one cybersecurity expert.
When it comes to cybersecurity, humans are the weakest link. Attackers often leverage on this weakness to gain access to sensitive data, carry out scams and perform fraud. Living in Singapore, with our low crime, effective security and strong legal system, people are often fooled into thinking the same of the internet world. Or they adopt the “who would target me?” syndrome.
But, the connected digital world means anonymous attackers can target anyone in the world. While the recent Singhealth breach made people aware of cybersecurity attacks, most still view cybersecurity as an organisational or state issue – not an individual one. However, cybersecurity is a personal issue. The cyber safety of organisations and a nation depends on individuals staying safe.
Attackers will continue to create new forms of attack, which exploit new vulnerabilities. In the past, we feared the IloveYou virus, Conficker worm and Wannacry ransomware. Crypto-jacking malware (which is the unauthorised use of someone else’s computer to mine cryptocurrency) have made headlines today. There will surely be new ones next year.
So what is the best way to stay safe? In today’s digital era, just about every aspect of our lives – from paying for food, to taking transport or connecting with friends – are somehow connected to the digital world.
A personal cyberattack is no longer a minor inconvenience, but something that could compromise your daily lifestyle. Fortunately, there are habits that you can cultivate to protect your digital lifestyle.

The first set of habits is to get your house in order. Your “house” refers to your computers and mobile devices.
HABIT #1: UPDATE YOUR SYSTEMS IMMEDIATELY
Turn on automatic updates and whenever you see a pop up, telling you to update, save what you are doing, run the update immediately and go for a break.
There are no perfect systems and software, as security researchers and attackers find vulnerabilities on a daily basis. But too many people put off system updates for another time, which exposes themselves to potential attackers.
HABIT #2: ALWAYS INSTALL AN ANTI-VIRUS
Whenever you get a new computer or devices, download and install anti-virus as your first software if they are not pre-installed. This applies to Microsoft PCs, Macs and Android devices.
Anti-virus prices are much cheaper these days with lots of good choices and bundle options. It’s a small investment compared to the price of your devices and the value of your personal information in these devices.
Once your house is in order, the next two habits safeguard the “keys” to your house – the passwords.
HABIT #3: USE LONG PASSWORDS
Passwords are meant to be secret, something only you know and are hard for others to find out. So avoid using easy-to-guess passwords like “123456”, common words from the dictionary or your personal information, like your date of birth. Good passwords are long and something only you can remember.
One recommendation is to use three words related to a special memory. For example, “bedokrainingdurian” would be easy for you to remember, if you tasted the best durian at Bedok on a rainy day.

HABIT #4: DON’T REUSE PASSWORDS
Just as we don’t share a secret with everyone, don’t reuse your password for different applications. This protects you against the scenario where attackers steal your login password from one website in a data breach, and subsequently use the collected data to login to other websites.
Famous data breaches where user login credentials are stolen include Yahoo!, Adobe and LinkedIn. You can check online if your email address has been compromised in a data breach.
And finally, you need to watch who is going in and out of your house. The remaining habits focus on cultivating safe web habits to keep away from unsavoury characters.
HABIT #5: WHEN NOT EXPECTED, DON’T CLICK
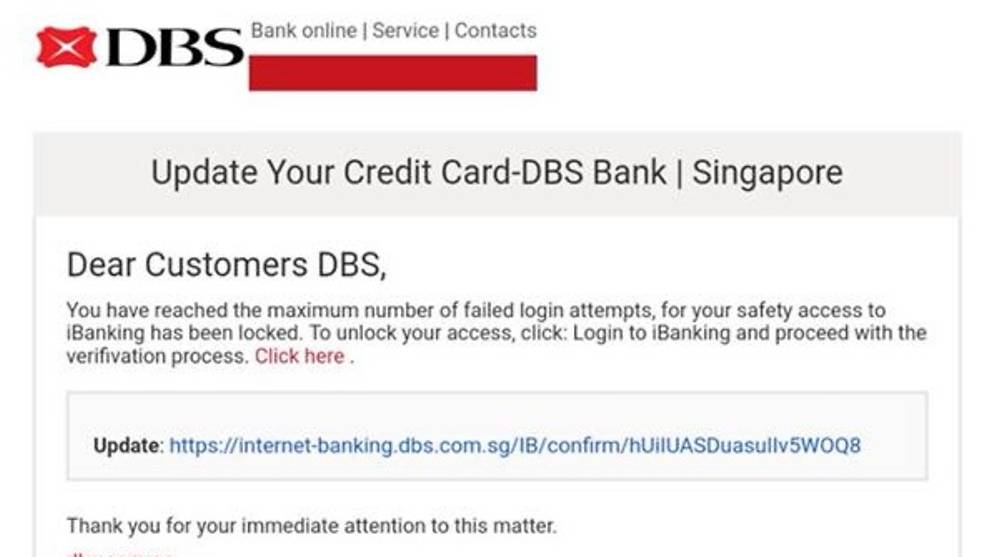
The most common way attackers target their victim is through sending phishing emails or messages. These are fraudulent attempts by attackers pretending to be someone else in an attempt to bait you to click links and download malicious software on your devices.
If you have not ordered a TV and a delivery man turns up with one, most people will be suspicious. Likewise, if you get an unexpected email address to a generic “dear sir/mdm”, the sender’s email address does not look right and he is asking you to click on links, don’t click. Don’t let them into your house.
HABIT #6: WATCH WHERE YOU SURF
When you visit a foreign country, good safety habits include staying on the main street, avoiding the alleys and dodgy establishments, and sticking with safe food choices. The same applies when surfing the web.
Only download software from official app stores by Microsoft, Google and Apple or legitimate sites. If you are unsure if it’s a legitimate site, Google the topic and legitimate sites will appear top.
Most legitimate sites will have HTTPS enabled (green padlock on browser bar) and the site will look professionally-built. If the site looks like a dodgy establishment, avoid it.
Be suspicious of sites with lots of pop-ups asking you to download and “Buy Now”. If a website tells you that you are infected with virus, don’t believe them.
Turn on safe browsing features on your web browser, which will warn you of fraudulent or unsafe sites.
HABIT #7: KEEP YOUR DIGITAL FOOTPRINT SMALL
Visiting social media platforms leaves behind your digital footprints. Whenever you share on social media, these digital footprints tell others who you are, where you are, how you can be contacted, whom you know and what you are doing.

Attackers collect your digital footprint to be more effective in their attack against you or the people you know. For example, a fraudster may use your children’s names, and their known whereabouts to conduct a scam against you.
Nowadays, people often share information on relationships, location data and contact numbers freely on social media sites.
Understand the settings on social media sites and make a conscious decision on who can see your posts – whether it’s your friends, your friends’ friends or the public. Keep your digital footprint as small as possible.
For those that want to stay safe online, get your house in order, safeguard the keys, and be careful of who you invite in.
Ng Pan Yong, founder of The Cyber Assembly, wrote this article originally as a guest writer for Channel News Asia.
About The Cyber Assembly
The Cyber Assembly provides various active learning platforms to help organisations and individuals connect to cyber skills, regardless of their gender, age, disabilities and qualifications. The Cyber Assembly is a startup under ICE71’s SCALE programme.
About ICE71’s SCALE Programme
SCALE provides the startup with opportunities to leverage a global network of investors, corporates and mentors to scale up its operations and expand further into the Asia Pacific market. In The Cyber Assembly’s case, they target ASEAN markets. Hence, we provide access to markets in the region through the ICE71 community, building other connections through NUS Enterprise and other government and corporate partners.
Source: CNA/nr(sl)