
Date: 27 Nov 2019

Date: 27 Nov 2019
According to a recent CSA report, businesses in Singapore lost nearly S$58 million to email impersonation scams last year. In the US alone, according to the 2018 Internet Crime Report, US$1.2 billion were lost due to email activities. So how can we be more cyber aware with regards to phishing attacks? One way is to conduct your organisation’s own phishing drill. Because if you are not doing it, the attackers are going to do so! Earlier this year at RSA APJ 2019, we were fortunate to hear from NUS’s CISO, Mr Ang on how to design effective phishing simulation drills.With more than 50,000 users and being a renown university, NUS is highly susceptible to phishing attacks.

An overview of a Phishing Lifecycle Drill
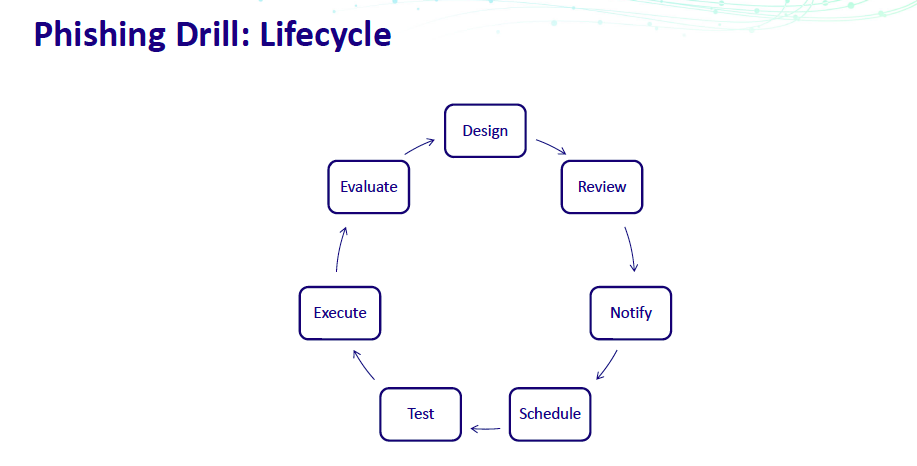
There are 7 steps in the lifecycle and we shall briefly examine each of the steps as shared by Mr Ang.
Design
You need to know
These are important as they define the whole simulation drill. There are also pre-drill and post-drill parts of the design phase, which aids in the effectiveness. Pre-drill could be sending out anti-phishing infographics, and post-drill could be sending out security advisory to the users who fell prey.
Review
Once you have designed a phishing drill, review to see if there are any sensitive content and/or obtain the necessary approvals. Sensitive content could be a simple “Your resort booking has been cancelled” message which may lead to the user thinking his or her credit card details had been compromised – resulting in card cancellation and police report being made. This might lead to undue stress on the user.
Notify
Notify the various departments in the pre-drill, during drill and post-drill phases. As always, communication is key but not in excess, as this will reduce the effectiveness of the drill.
Scheduling
When scheduling a drill, do note the working hours, day of the week, holidays, rate limits and duration. In terms of day of the week, for example, sending a phishing email on a Friday evening tends to be ignored. This will impact the results.
Test
Test the drill with a small group of users first, verifying the look and feel. Ensure all links are working and verify the recipient list.
Execute
Prepare for user queries and scripted answers for your IT helpdesk, as they maybe overwhelmed with queries once the drill has been executed.
Evaluate
This is essentially what to look out for after you have completed the drill. Compare your results with industry benchmarks, if any. Compare results across departments and against previous drills. Of course, identify users who repeatedly fall prey and send them for compulsory education trainings.
If you’ve been wondering how to get started with a phishing drill, wait no further. Start from the design process!
For more updates like this, follow ICE71 on our web and social channels.